Note: QuantumReady Consulting is a working name only for this draft site. It is not the final chosen company name.
Sensitive data is already being intercepted and stored today, waiting for quantum computers to make it readable.
If your data needs to remain secure for years, and your migration will take years, you may already be exposed. We help organisations start with discovery, analysis, prioritisation and transition planning so they can act before time runs out.
Australian Signals Directorate (ASD) recommended target milestones for becoming post-quantum cryptography safe:
Attackers do not need quantum computers today to put your organisation at risk. They are already using a strategy known as Harvest Now, Decrypt Later, capturing encrypted data now and storing it until quantum computers can break today’s encryption.
That means data stolen today may be decrypted years from now. For organisations holding sensitive customer, financial, health, legal or government-related data, the exposure window is already open.
Encrypted data is intercepted and stored.
Quantum capability matures and current encryption becomes vulnerable.
Previously secure data becomes readable and misuse becomes possible.
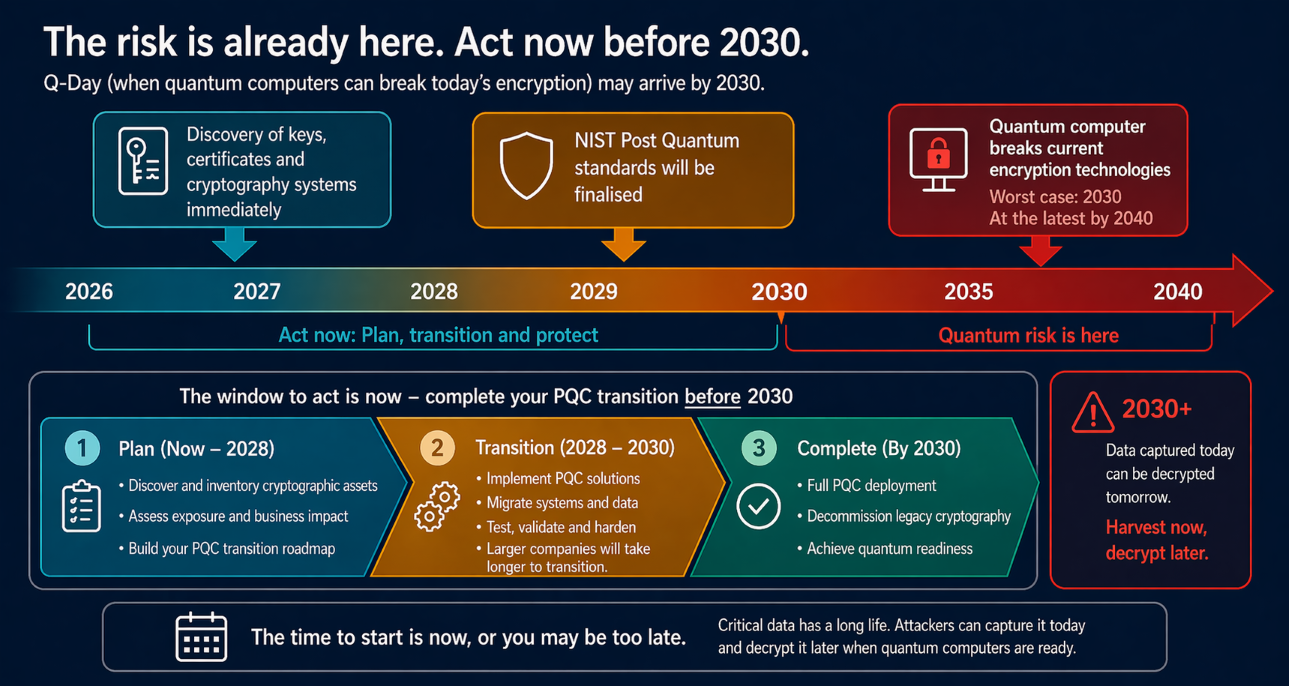
Quantum computing is not only a technology problem, it is a timeline problem. If your data needs to stay secure longer than it will take your organisation to complete migration, you are already behind.
Migration to quantum-safe cryptography can take years across complex applications, infrastructure, networks, APIs and vendor platforms.
Customer data, financial records, identity information, health records and intellectual property often need confidentiality well beyond the likely arrival of practical quantum capability.
The first challenge is not remediation. It is discovering where traditional asymmetric cryptography exists and understanding what it protects.
Quantum computers have the potential to break through and expose company and customer data protected by nearly all commonly used forms of traditional asymmetric encryption. This reaches across data at rest and data in transit, including storage, network traffic, Wi‑Fi, end user devices, databases, APIs, certificates and system-to-system communications.
Anyone responsible for company data, customer data, regulatory exposure or reputational damage from a breach should care about this now.

This is not a certificate refresh or a patch. It requires identifying every use of cryptography across your organisation and understanding what data it protects.
For most organisations, this becomes a multi-year programme across applications, infrastructure and vendors. That is why the right place to start is structured discovery and assessment.

Delaying increases both risk and cost.
The question is no longer when to start. It is how much risk you already carry.
Not all organisations face the same level of quantum risk. Organisations need to quickly understand the risk factors that quantum computing may pose to their business operations and security. Every organisation that holds and processes sensitive data should consider the lifetime value of that data, and the impact of that data being exposed or misrepresented by bad actors in the future.
Most organisations will take years to identify, prioritise and migrate cryptography safely. Waiting reduces your available time to act.
The risk is not only future decryption capability. It is the current need to find where traditional asymmetric cryptography already exists, understand what it protects, and work out how long a safe transition to quantum-safe encryption will take.
Sensitive data stolen today may still be valuable in the future, particularly where confidentiality needs to hold for many years.
Cryptography sits in certificates, libraries, APIs, cloud services, hardware, partner integrations and vendor products that are rarely tracked end to end.
Large organisations need time to assess risk, sequence change, coordinate vendors and transition without breaking critical services.
These questions help explain why quantum readiness, cryptographic discovery and post-quantum transition planning are now becoming enterprise priorities.
Post-quantum cryptography refers to cryptographic algorithms designed to remain secure against future quantum computing attacks.
Timelines vary, but organisations are preparing now because attackers may already be stealing encrypted data today with the intent to decrypt it later.
Quantum readiness is the process of identifying where vulnerable cryptography is used, assessing risk, prioritising remediation and planning a transition to quantum-safe encryption.
Without a cryptographic inventory, you cannot see where traditional asymmetric encryption is used, which systems are exposed and what should be prioritised first.
Because the risk is already active. Attackers are collecting encrypted data today using harvest now, decrypt later strategies, and organisations with sensitive long-life data face the greatest exposure. At the same time, migrating to quantum-safe cryptography can take years across complex environments.
For most organisations this is a multi-year transformation involving discovery, risk assessment, roadmap development and phased migration across systems, platforms and suppliers.